Hi everybody,
It has been a busy month since our last post, so here is a recap of some new features that we have released for PandwaRF.
Brute Force:
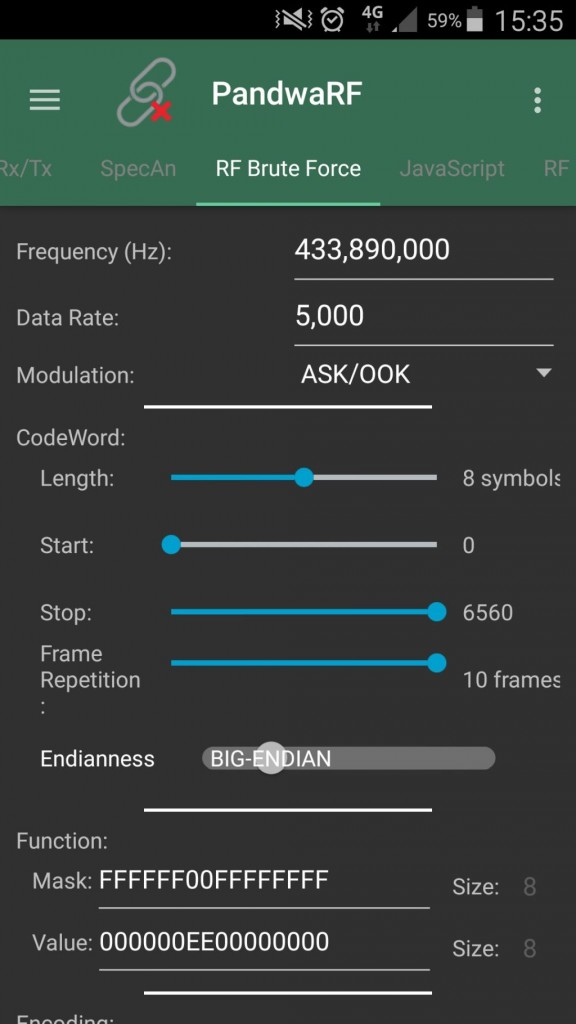
You may have seen the last improvement in the Brute Force feature of our app.
-
- PandwaRF now handles frame repetition internally. As many devices require several frames to be sent before doing something, this can be very handy.
- You can also choose the endiannes of the transmission, eg. MSB or LSB first.
- We have also introduced a very useful feature: the Function Mask. Basically it consists of a huge bit mask indicating to PandwaRF how to distinguish device Id bits (the one to brute force) from function bits (eg. Arm/Disarm) which are not to be brute forced.
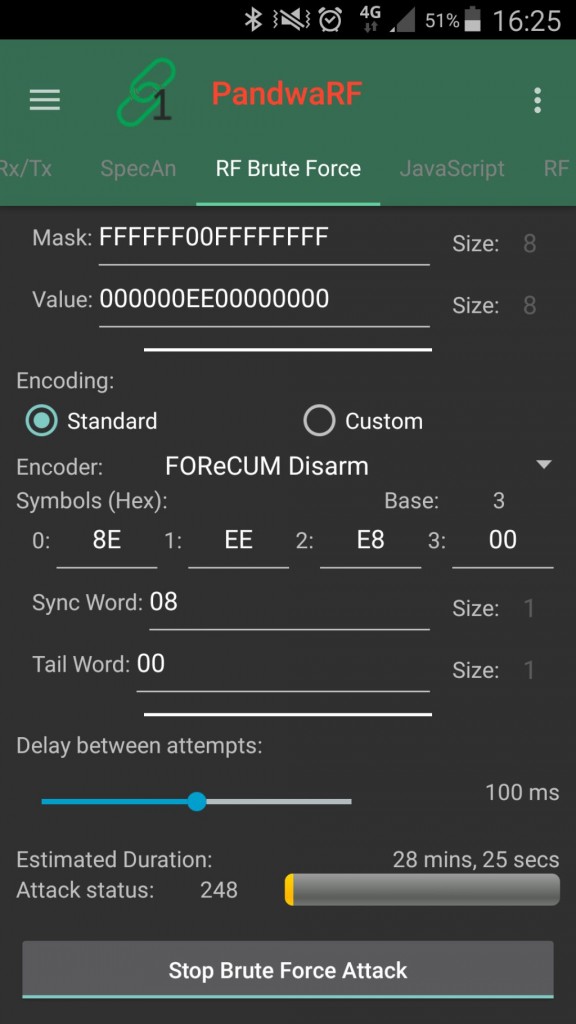
- PandwaRF now supports brute forcing in base 2 or 3, as many low cost remote controls are using base 3 encoders.
We recently uploaded a video showing the Brute Forcing of an alarm system.
You asked for an Android SDK, and it has been long awaited, but the time has come. In the coming days you will find in our wiki some Android sample applications on how to use the main features of PandwaRF: RX, TX, Spectrum Analyzer, JavaScript.
We are also halfway to launching the PandwaRF Rogue, a device dedicated to RF brute forcing for penetration testing.
The PandwaRF Rogue version is an improved variant of the PandwaRF, ideal for brute forcing wireless devices available on the market. It is based on the same HW as PandwaRF, but with many SW optimization and fine tunings. The embedded Brute Force engine has been reworked to reduce the brute force duration.
We’d love having your feedback on our work, so please don’t forget about our survey. It’s a great way to share with us your thoughts on PandwaRF so that we can know what to focus on in the future.
Thanks for reading and stay tuned!