Kaiju now supports the decoding and generation of Seed based KeeLoq models FAAC SLH and Genius Amigo.
These models operate on 433/868 MHz and are commonly found across all Europe.
KeeLoq Secure encryption
FAAC and Genius both use a KeeLoq Secure encryption, which is based on a random seed exchanged only once – during the pairing process – between the keyfob and the receiver.
The seed is then transformed into a device key which is used for every transmission between the keyfob and the gate opener receiver.
These seed is only known to the remote and the receiver, and never exchanged again, making difficult for an attacker to decrypt the intercepted data.
Master/Slave SLH protocol
On top of that another security mechanism called SLH master/slave protocol has been introduced in the SLH remotes.
The master/slave SLH protocol is mainly found in buildings or condominium units. Typically the property manager has a master SLH remote, while the tenants have a slave SLH remote.
Only the master SLH remote is able to generate and transmit a random seed to a slave SLH. Thus a tenant with a slave SLH cannot create a new remote without the manager’s approval.
Using the KeeLoq Secure Decrypt feature from Kaiju, you can now decipher transmissions from both master or slave SLH keyfobs.
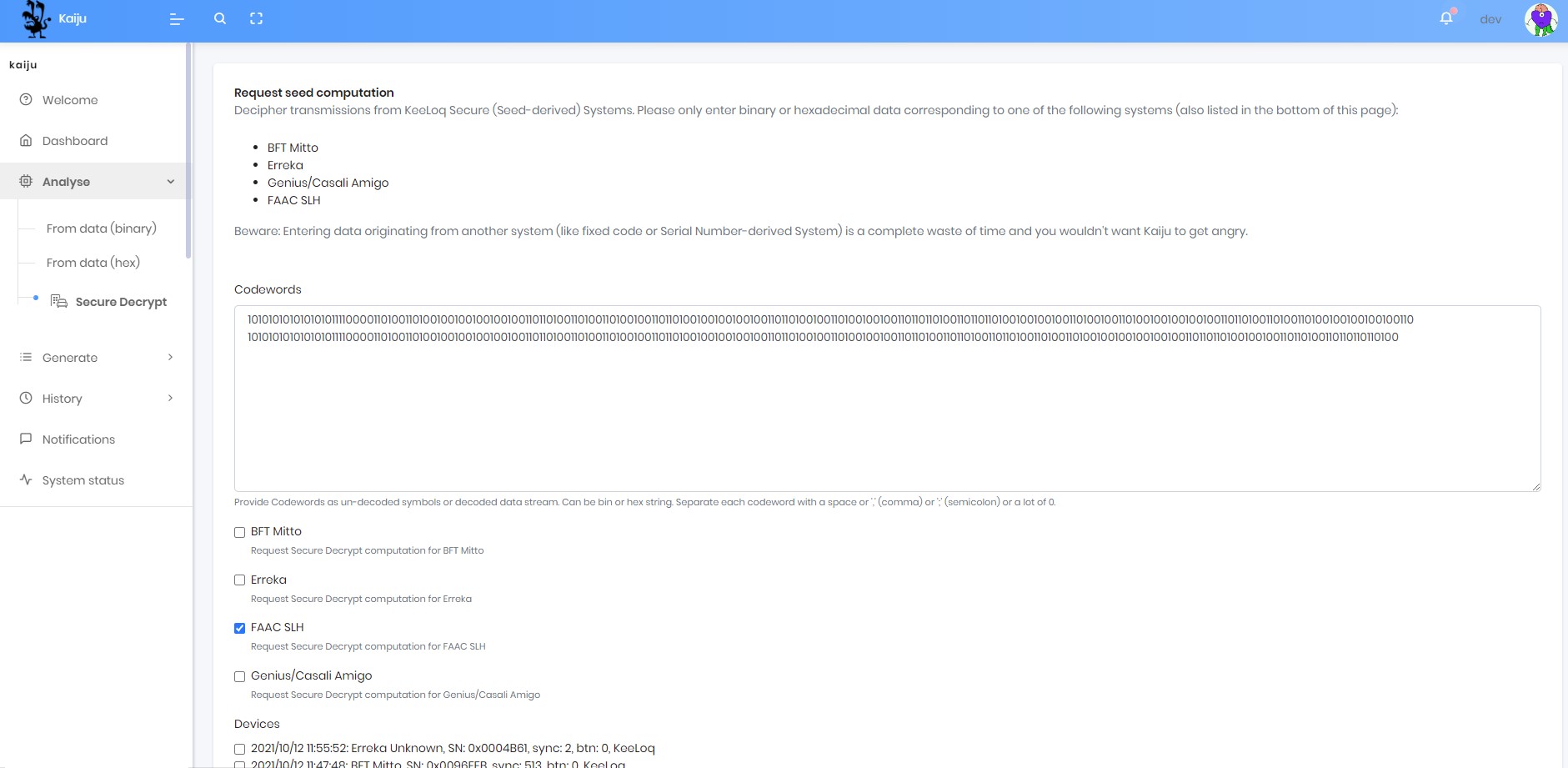
Using Kaiju Secure Decrypt
- Using PandwaRF, capture a RF transmission from a SLH remote
- Alternaltively you can capture this data using a SDR (HackRF, RTL-SDR, USRP, etc…)
- From the Analyse/Secure Decrypt menu, simply paste the captured data (binary or hex) from a SLH keyfob into the Codewords input box.
- Alternaltively you can select one or more previously captured remotes (you need to be sure it is a FAAC SLH remote) and use them as the input for decryption
- Then select the “FAAC SLH” checkbox to request Secure Decrypt computation for FAAC SLH.
- Kaiju needs to know the brand of the keyfob to successfully decode it.
- Selecting another brand (eg. BFT Mitto) if the codewords are from a FAAC SLH remote is a waste of time and the breaking process will be longer than selecting only the correct brand (FAAC SLH).
- Click Compute to start the decryption process
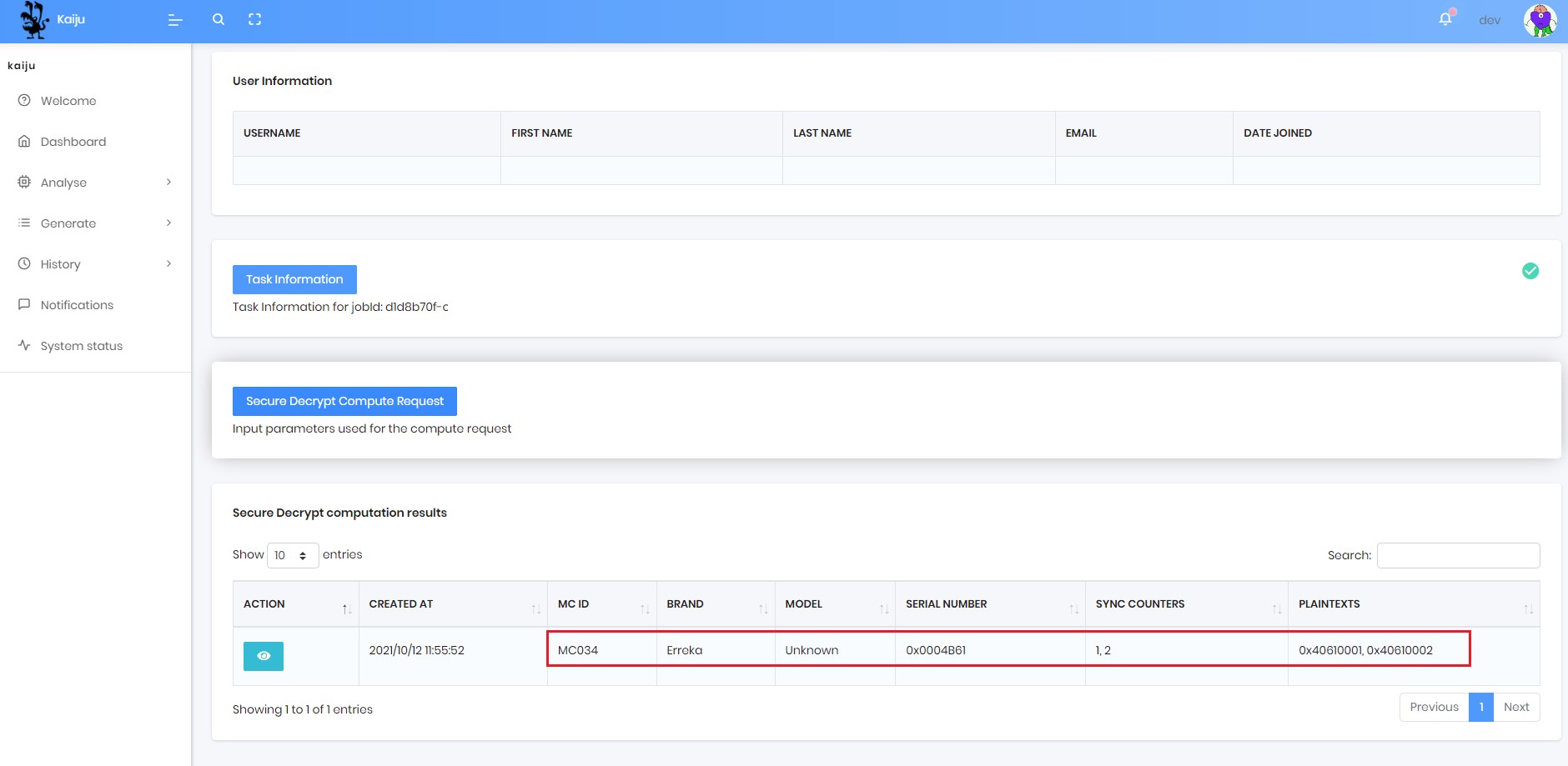
- The decryption can take between 2 to 10 minutes, based on your priority in the processing queue
- When decryption is finished, you are redirected to the Secure Decrypt page where the decryption results (Serial Number, Sync Counters, PlainTexts, etc…) are displayed
- Alternatively, you can retrieve all previous decryption results in History/Secure Decrypt
We have worked hard to make all the decryption process as simple as possible for the user, so please let us know what you think of this feature, and stay tuned for other cool hacks.
If you are from a LEA, you can contact us directly to learn more about the new powerful attacks reserved for Police and Governements.