We just uploaded a video where we explain what happens when you use the brute force feature of the PandwaRF.
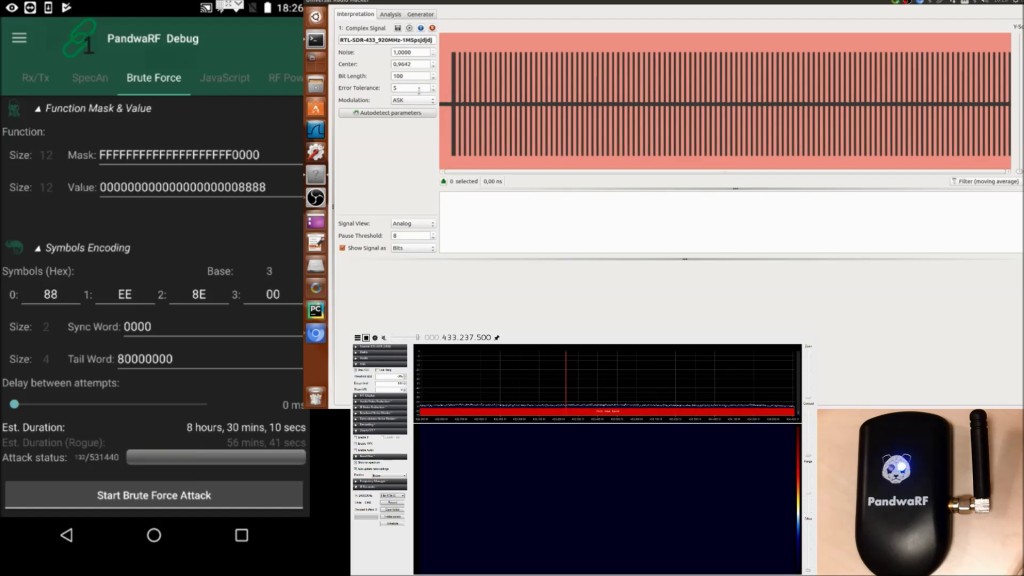
The setup was composed of:
- one PandwaRF device (in the demo we used the public version of PandwaRF, but for advanced brute forcing we recommend using the PandwaRF Rogue Pro)
- the Android application
- one RTL-SDR dongle connected to SDR#
- another RTL-SDR dongle connected to Universal Radio Hacker
We started by explaining the parameters of the brute force fragment in the application: endianness, function mask and value, symbol encoding etc.
We then launched a brute force attack and we analyzed the data using SDR# and Universal Radio Hacker.
The purpose of the demo was to understand the connection between the settings of the brute force fragment and the final data by visualizing the result.
If you liked this video, make sure to also check out our other demos on how to capture and retransmit data using several modulation patterns and how to perform a replay attack.
Thanks for watching!
Disclaimer: You may only use the brute force feature to assess the security of your own RF devices. You are solely responsible for using your PandwaRF legally.