Not long ago the French magazine Auto Plus contacted us because they were interested in writing an article on the security of garage doors. They wanted to show their readers how easy it is to break into a garage without leaving a trace.
The remote controls used to open garage doors can either have a fixed code (about 50% of them) or a rolling code.
- The fixed codes are the least secure and can be hacked using a capture and replay of the code or a brute force attack.
- The second one, the rolling codes, change at every usage of the remote control which makes them more secure. However, they can still be hacked by jamming the signal sent by the owner, which this way never gets to the receiver and can still be captured and used afterwards to open the door. This attack is known as “Rolljam”, originally demonstrated by Samy Kamkar.
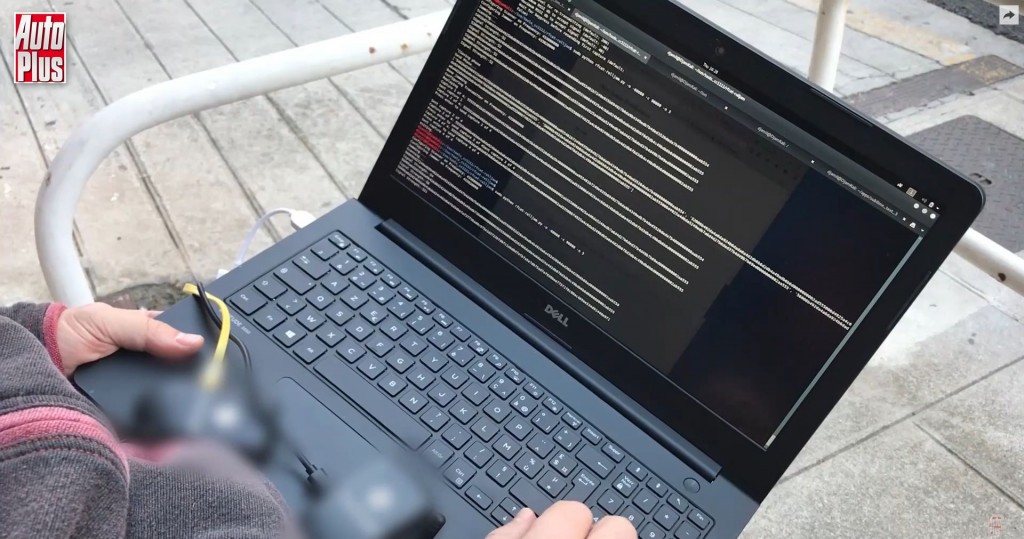
When preparing the article we started by explaining to the Auto Plus team the basic RF concepts and then we performed a live demo on a garage door using 2 setups:
- 1x PandwaRF controlled by an Android Smartphone. This setup was used for the replay attack.
- 2x PandwaRF, each controlled by a Rolljam Python script running on Linux. This setup was used for the “Rolljam” attack.
The remote control was operating at 433.92 MHz, in 2-FSK modulation.
Auto Plus documented the entire operation in the article, followed by a few tips for the readers to prevent their garage from being hacked. But the purpose of this investigation was also to alert the companies selling garage door remote controls regarding the (lack of) security of these systems.
We hope we managed to shed some light on the issue and make people a little more aware of the risks.
You can find a preview of the article here and the full article (in French) here. French readers, you can still find the magazine in the news stands until Thursday 🙂