We are happy to announce that 2 new features are available for PandwaRF Rogue Pro and Gov:
- Automated Data Analysis
- Function Inversion
These features can be used by an attacker to perform an enhanced RF replay attack.
You might already be familiar with classic RF replay attacks, where the attacker simply replays a RF frame previously captured. This only works in cases where the action (aka function) the attacker wants to transmit has already been captured.
But with the combined usage of Automated Data Analysis and Function Inversion, we are proud to bring replay attack to the next level.
With these 2 features used sequentially, the user, after capturing any data from the target’s remote control, can find what brand/model the data is being captured from, and impersonate any command from this device.
The scenario is as follows:
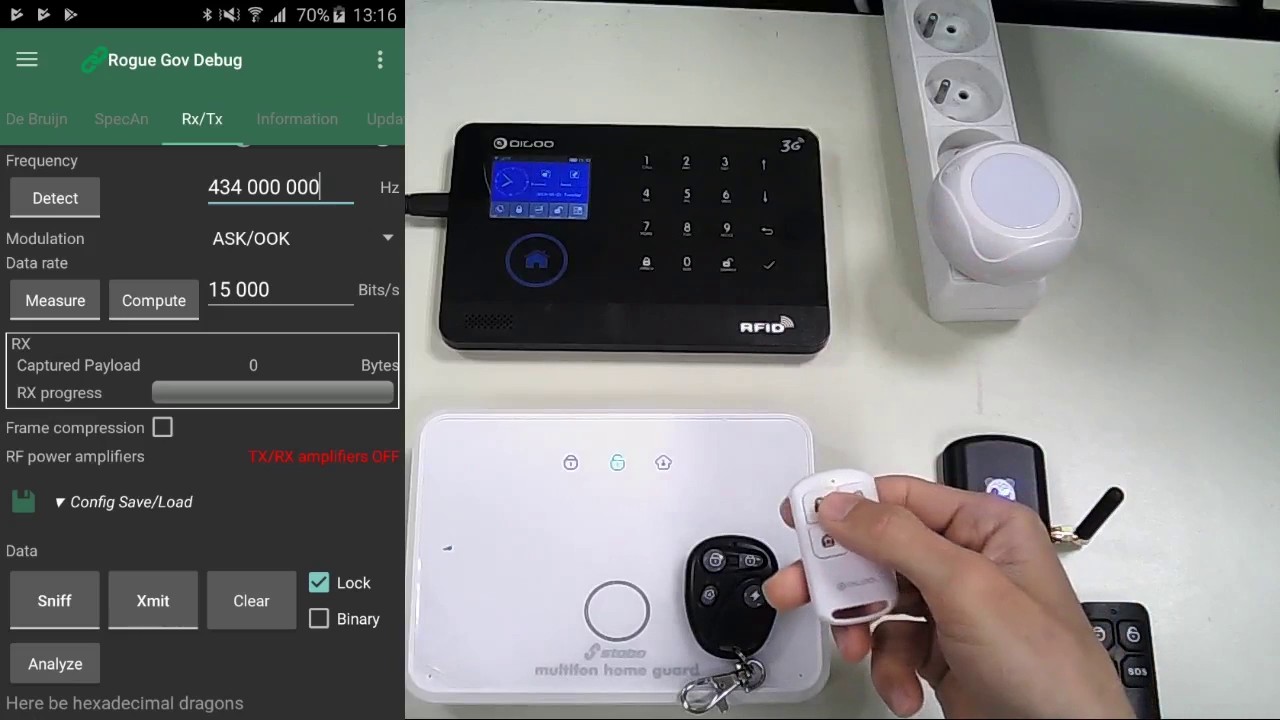
- the attacker starts capturing RF data
- the target uses its remote control and sends an Arm command to its home alarm (or other device)
- once the data is captured, the attacker starts post-analysis by using the Analyze button
- the attacker impersonates the target’s device, and sends a Disarm to the home alarm, having never received a Disarm frame before
In the demo video you will see how to use the Model searcher.
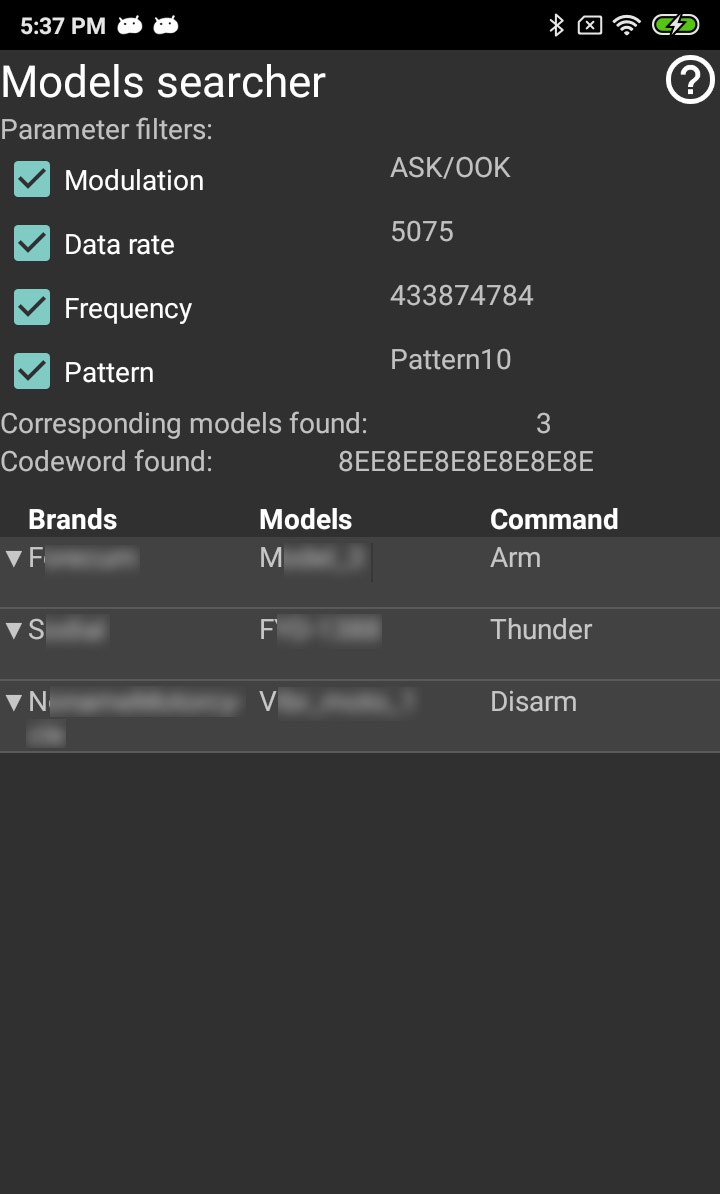
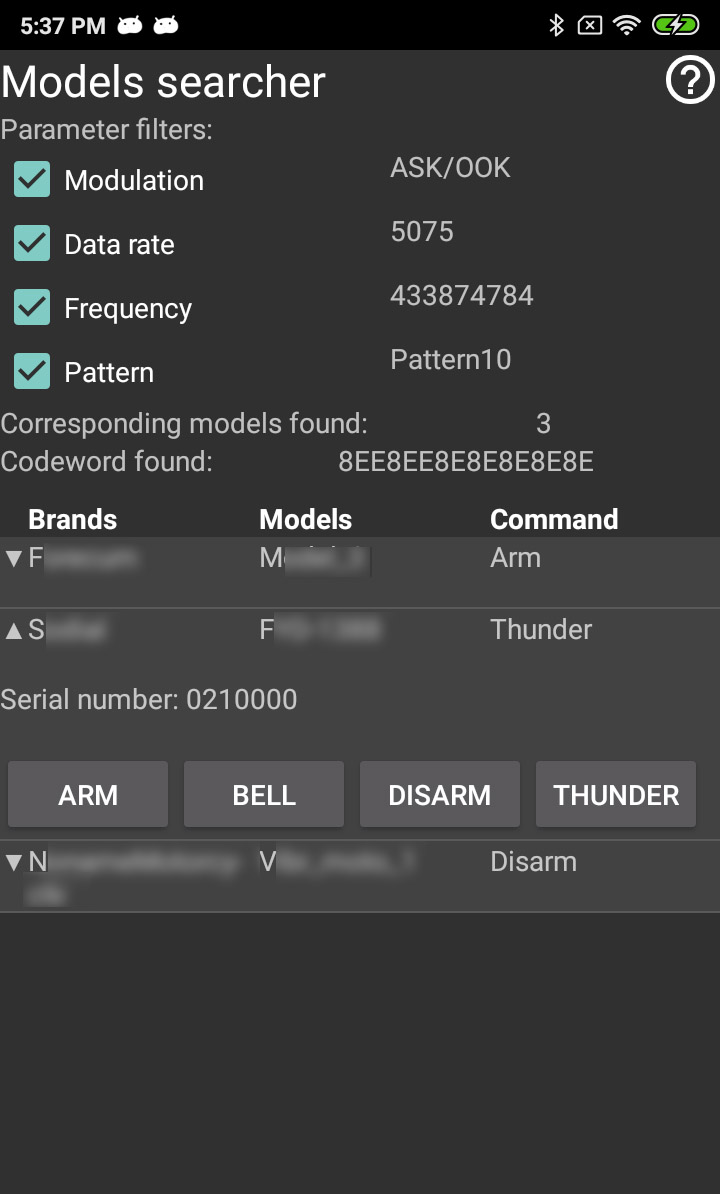
The Model searcher processes data and displays:
- the captured codeword, filtered to remove noise and glitches
- 4 filters (Modulation, Data rate, Frequency and Pattern) to fine tune the results if needed
- the number of corresponding devices found
- a list of corresponding devices with:
- the brand and model of the device
- the meaning of the captured command for this model (Arm, Disarm, etc…)
- a list of possible actions that can be used to impersonate this specific model
All items in the list can be expanded to display the serial number of the captured remote and all the commands (buttons) that can be impersonated.
When the attacker clicks on a button from the PandwaRF Rogue Gov application, the fake command is sent by the Rogue Gov as if it was originating from the target remote control, and the target receiver is fooled.
In case the Model searcher doesn’t find a corresponding model, some filters can be unchecked to broaden the number of corresponding models.
For example if you uncheck the frequency filter and if a device matches all the other filters, it will appear in the list, regardless of the frequency value.
To be sure of the accuracy of the list it’s preferable to activate a maximum of filters.
There are many advantages when using this feature:
- you can know all the information about the device after only receiving one command from the device
- you can replay any command as you wish
- it is easy to use and it does not require almost any RF knowledge
Here is a demo video showing the Automated Data Analysis and Function Inversion.
Update June 4, 2019: We also uploaded a demo video showing how to use this feature on gate openers.
Our conclusion:
- Some home alarms are cheap, but not reliable against a determined/well equipped attacker.
- If we can break it, so can they. Using the Rogue Gov you can assess the security of your alarm systems before it’s too late.
If you can’t wait to try it out yourself, good news! For Rogue Gov orders placed until May 31, a commercial alarm for demo & testing is also included. Contact us for more information.
(*) While being present in all the PandwaRF Rogue family (Pro and Gov), the Automated Data Analysis and Function Inversion features rely heavily on the device database. Please note that due to the sensitivity of this feature, the full device database is only available for PandwaRF Rogue Gov. The PandwaRF Rogue Pro contains a DB with supported chipsets, not commercial devices.
Disclaimer: Remember the scenario below is for usage on your own equipment. You are solely responsible for using your PandwaRF Rogue legally.