I have been working on rolling code support for a long time now, and progress have not been as fast as I would have foresee in the beginning.
I must admit that I largely underestimated the reverse engineering work to be done to support hundreds of brands and models.
It took me a lot of time capturing keyfobs RF transmissions, dumping firmware from various devices, analyzing binaries with tools like Radare2 or lately Ghidra.
But I have learnt a lot, and my skills in FW analysis have made a huge step forward (note that I am still considering myself a newbie, given the huge possibilities of Ghidra).
I really think reverse engineering is much more effective in teamwork, so thanks to all folks who helped me a lot in understanding some tricky encryption schemes (thank you Derrow).
Working on this alone would have taken much longer.
The good news is that we are close to support a large amount of gate openers rolling codes.
Among the supported devices, some major brands like Sommer, Merlin, JCM, AERF, etc…
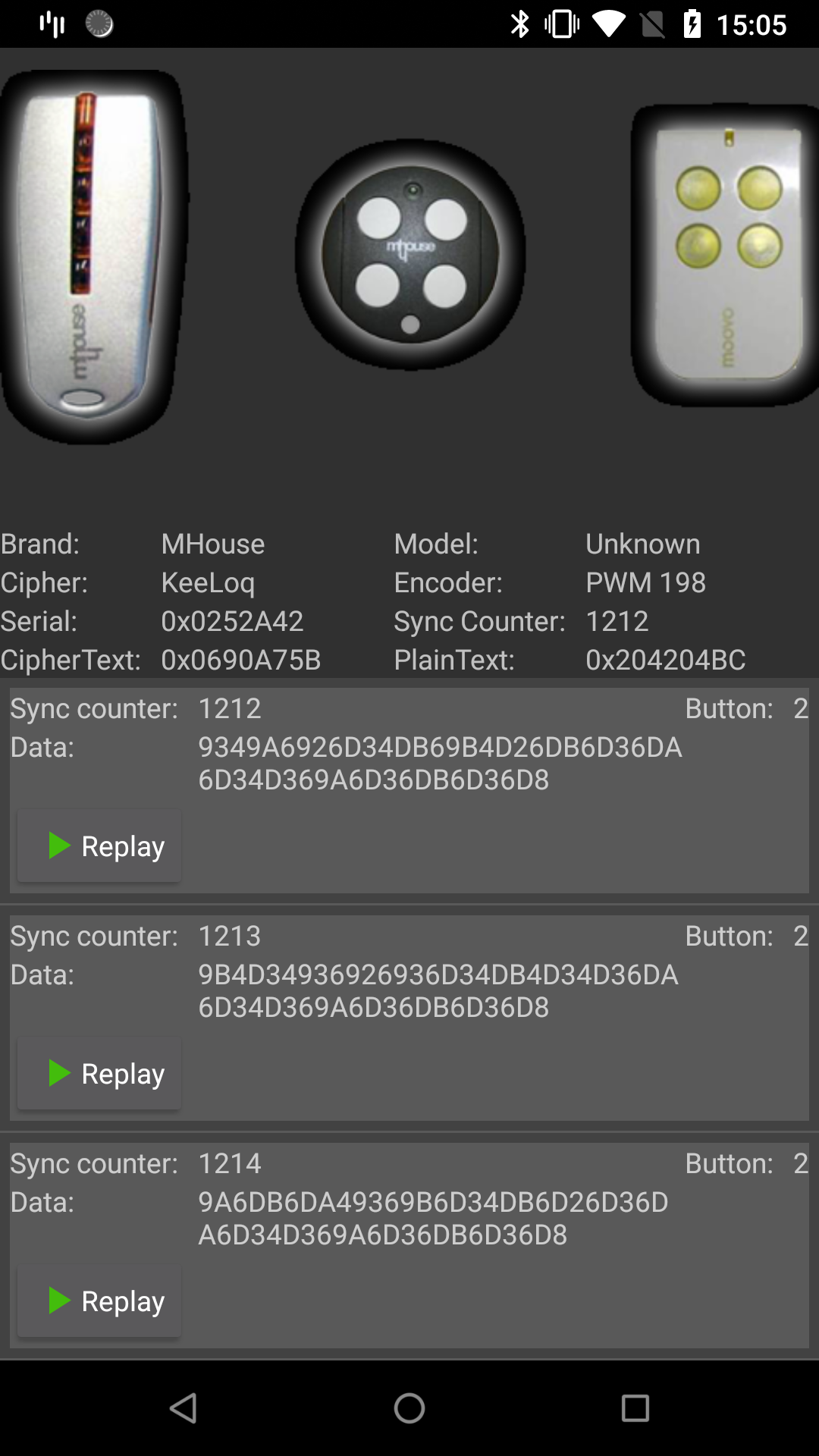
Many of them use the KeeLoq encryption scheme, but not only. I have been surprised to find out that some manufacturers added their own custom encryption on top of KeeLoq. This doesn’t make the transmission more secure, so I am a bit skeptical why they have done this.
To thank you all Rogue customers that have been very patient since the beginning, the rolling code support will be available once ready to all the existing Rogue Pro, Rogue Gov, and Marauder Ultimate, until stock lasts. So hurry up.
[Update] The Rolling code processing is in Alpha version since PandwaRF Android App v1.7.0. The limitations are that the data must be captured at the correct data rate (sampling rate = data rate), because our algorithm is not yet capable of down sampling data. This will be integrated in next release.
The database of supported gate openers brands & models will continue to grow as I spend more time on device reversing.
But you may have noticed that I only mentioned gate opener devices. Gate openers will be the first subset of devices to be released, but I am planning to work next on car keyfobs.
I will keep you updated on the status.
To all fellow HW hackers: if you have some FW to analyze, you can always contact me. I would be happy to work with you on reversing them and integrate them in our list of supported brands. Plus you may get some free PandwaRF Rogue… 🙂
[Edited on Sept 18, 2020 to update status]
PS: link to Kaiju – Rolling code analyzer & generator