We just uploaded a detailed tutorial on implementing a new brute force in the PandwaRF Android application – from identifying the frequency of the signal to launching the brute force attack.
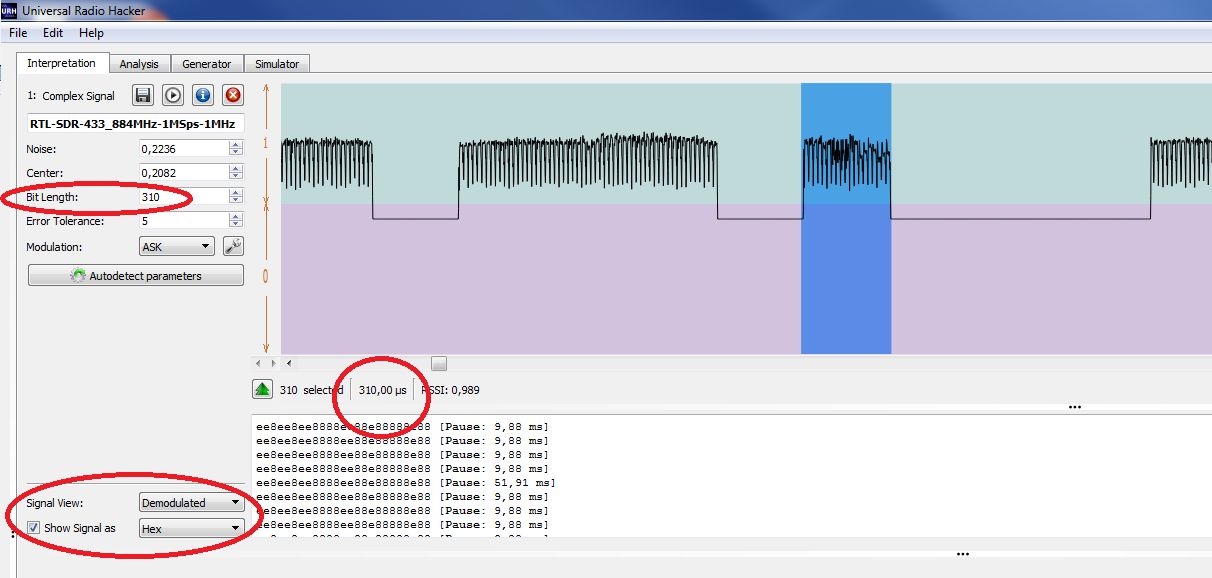
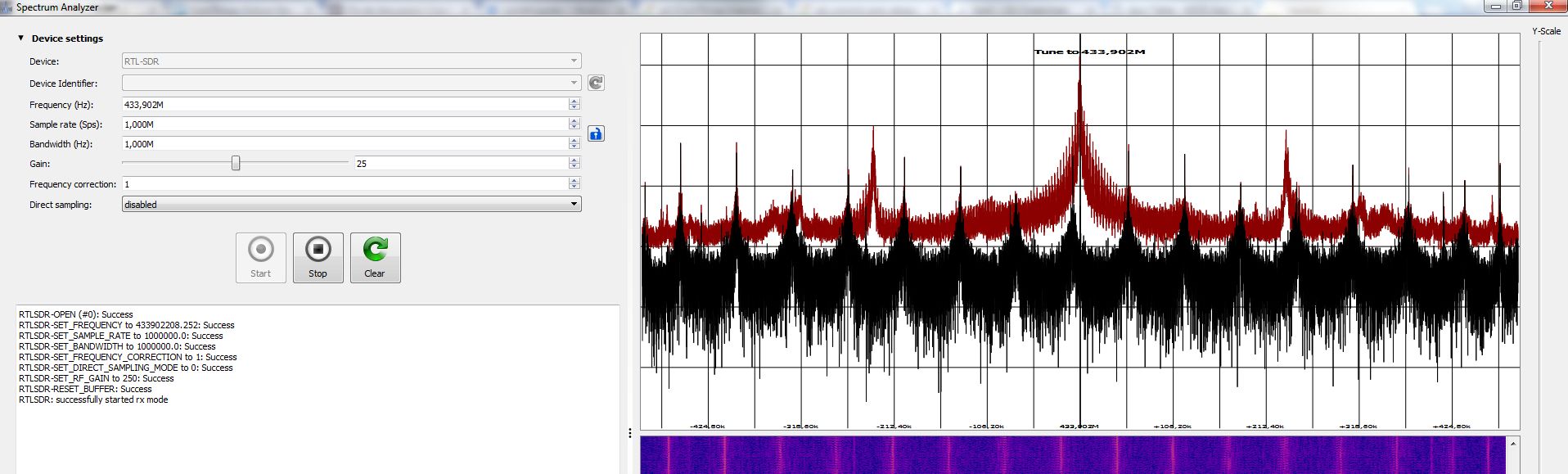
We started by showing you how to capture and interpret data from a remote control using Universal Radio Hacker (URH): identifying the frequency, recording and interpreting the signal. Here you will learn how to decompose the signal into codewords and how to find the synchronisation word, the tail word and so on.
The second part of the tutorial focuses on the Brute Force feature of the PandwaRF application: understanding the parameters you need to fill out in order to successfully perform a brute force attack. We explained terms like symbols, frame repetition, function mask and value, delay between attempts etc.
You can find the full tutorial in our wiki. Afterwards you should be able to brute force a new device, but remember that you may only use it to assess the security of your own devices 🙂
Also, don’t forget about our device bounty. By sending us your data you can earn a PandwaRF, a PandwaRF Rogue Pro or a discount on one of our products. Every submission gets rewarded!
Happy RF hacking 🙂